6 Essential Security Features for AI Agents in HashiCorp Vault
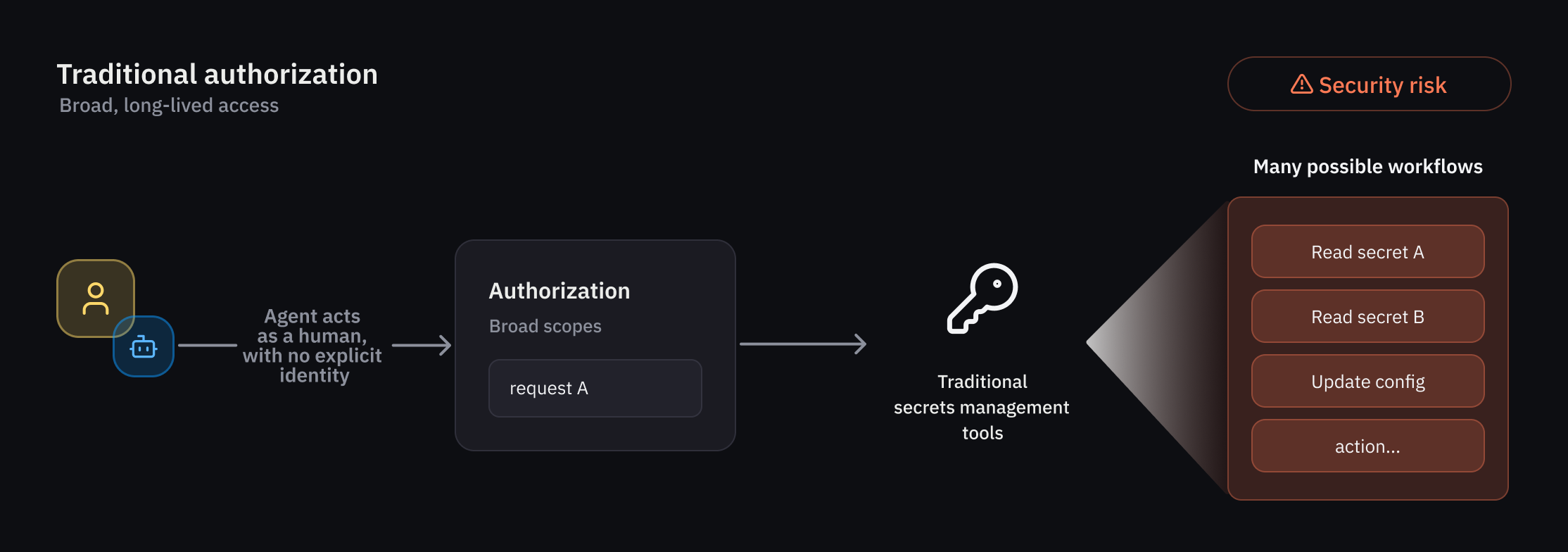
As organizations integrate autonomous AI agents into their workflows, traditional IAM frameworks struggle to keep up. These agents operate nondeterministically, often acting on behalf of human users, and require a fundamentally new authorization model—one that combines identity, delegation, runtime policy evaluation, and ephemeral permissions. HashiCorp Vault has introduced native support for AI agents to address these challenges. Below are six critical capabilities that redefine how security teams manage and govern autonomous identities.
- Agent Registry for Distinct Identity Management
- Granular Identity-Based Policies for Least Privilege
- Per-Request Ephemeral Authorization
- Delegation and Consent Tracking
- Runtime Policy Evaluation for Non-Deterministic Behavior
- Early Access Program and Future Availability
1. Agent Registry for Distinct Identity Management
Vault’s new agent registry allows developers to register and manage AI agents separately from human users and traditional non-human identities (NHIs). This separation is crucial because agent behavior is less predictable and often involves delegation—for example, an agent acting on behalf of a human via an on-behalf-of (OBO) pattern. By maintaining a dedicated registry, organizations gain clear attribution and auditability for every action performed. The registry serves as the foundation for authorization, credential management, and observability, ensuring that agent activity is explicitly tracked and never mixed with human or system identities. This precise delineation reduces attack surface and simplifies compliance audits.
2. Granular Identity-Based Policies for Least Privilege
Least privilege access is a top priority, especially for autonomous agents that can behave unpredictably. Vault provides a rich set of policy-based runtime controls that allow administrators to define deterministic guardrails around agent actions. Policies are tied directly to the agent’s identity, enabling fine-grained rules such as “this agent can read secrets only from a specific path and only between 9 AM and 5 PM.” Because agents may delegate authority from a human user, policies must evaluate multiple trust dimensions—including the user’s original consent and the agent’s scope. This layered approach ensures that even if an agent goes rogue, the blast radius is contained.
3. Per-Request Ephemeral Authorization
Traditional static permissions are a poor fit for transient, task-oriented agents. Vault introduces per-request ephemeral authorization, granting temporary access rights that expire after a specific task or timeframe. For each request, Vault evaluates the agent’s identity, the delegated authority, and the context of the operation before issuing a short-lived credential. This reduces risk by eliminating standing privileges and ensuring that even if credentials are intercepted, they cannot be reused beyond their intended purpose. The system automatically revokes access once the operation completes, aligning with zero-trust principles and minimizing exposure.
4. Delegation and Consent Tracking
AI agents frequently operate in delegation mode, carrying the authority of a human user. Without explicit tracking, this can lead to privilege escalation or unauthorized actions. Vault’s agent registry and policy engine enforce consent-based delegation: every OBO flow requires clear consent from the delegating user, and that consent is logged and verifiable. Administrators can see exactly which user authorized which agent to perform which action. This audit trail is critical for compliance (e.g., SOC 2, SOX) and for incident response, as it provides a complete chain of custody from human to agent to target system.
5. Runtime Policy Evaluation for Non-Deterministic Behavior
Because agents may explore different paths based on real-time data, their behavior is non-deterministic. Vault handles this by applying deterministic policy evaluations at runtime, checking each action against predefined rules just before execution. This allows organizations to define guardrails that are flexible enough for agent experimentation but strict enough to prevent policy violations. For example, a policy might allow an agent to read any secret in a project namespace, but prevent writes to production credentials. The runtime engine evaluates these conditions on every request, adapting to the agent’s actual without granting open-ended permissions.
6. Early Access Program and Future Availability
Select customers are currently evaluating these capabilities through an early access program. Broader public beta availability is planned for a future Vault release this summer. This phased rollout allows HashiCorp to gather real-world feedback on agent identity management, policy enforcement, and ephemeral authorization before general availability. Organizations interested in securing their AI agents are encouraged to join the early access program to gain firsthand experience with these advanced controls. The final release will include documentation and best practices for integrating AI agents across hybrid and multi-cloud environments.
Conclusion
As AI agents become integral to business operations, traditional IAM falls short. HashiCorp Vault’s new native support—spanning agent registration, granular policies, ephemeral authorization, and delegation tracking—provides the robust, adaptable security foundation that modern autonomous workflows require. By embracing these capabilities, organizations can safely empower AI agents while maintaining strict governance and auditability.