Uncovering the Secrets of Hard Drive Firmware Modification
Introduction
Most computer users are familiar with updating firmware for devices like routers, smartphones, or graphics cards. But when was the last time you thought about hard drive firmware? For the average person, the idea of tampering with the code that controls a spinning hard drive (or even an SSD) is daunting—and usually unnecessary. However, a niche community of hardware hackers and reverse engineers has found compelling reasons to dive deep into this hidden layer. One such example is the work of [I Code 4 Coffee], who used hard drive firmware manipulation as part of a clever exploit for Xbox 360 consoles. This article explores the process, tools, and insights gained from reverse engineering hard drive firmware.
Understanding Hard Drive Firmware
Firmware is the low-level software embedded in hardware that tells the device how to function. For hard drives, firmware controls everything from reading and writing data to managing cache, handling errors, and communicating with the host computer. While most users never need to update it—manufacturers only release updates for critical bugs—modifying firmware can unlock hidden capabilities or enable unconventional uses.
Why Modify Hard Drive Firmware?
Typical reasons include data recovery, repurposing old drives, or exploiting security loopholes. In the case of [I Code 4 Coffee], the goal was to use hard drives in a way that allowed unauthorized modifications to Xbox 360 consoles. This required understanding and altering the drive's firmware to execute commands that a standard operating system would block.
The Xbox 360 Exploit Connection
The Xbox 360, like many consoles, has stringent security measures to prevent pirated games or homebrew software. However, hard drives connected to the console can be a vector for attack if their firmware can be reprogrammed to behave in unexpected ways. [I Code 4 Coffee] began by gathering three conventional hard drives and one SSD to experiment with. The hope was to find existing research or tools that could streamline the process—but the available information was sparse and often outdated.
Tools and Techniques for Firmware Analysis
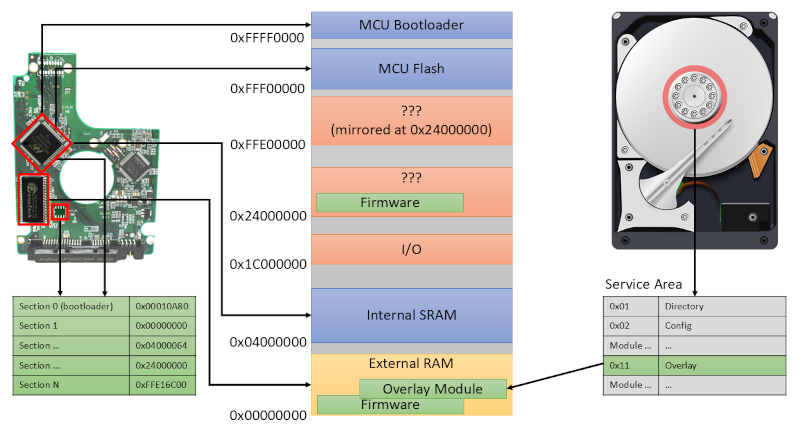
Without a large public database of hard drive firmware modifications, the team had to rely on specialized hardware and software. One key tool was the PC-3000, a professional data recovery system that can read firmware dumps from many drive models. These dumps contain the complete firmware code and configuration data, which can be analyzed offline.
PC-3000 and Firmware Dumps
Using the PC-3000, [I Code 4 Coffee] obtained firmware dumps from their test drives. This process involves connecting the drive to the recovery unit, which bypasses normal operating system restrictions. The raw firmware image can then be disassembled or patched. The artifacts from this work have been published on GitHub for others to study.
Backdoor Commands and RS-232 Diagnostic Port
During the reverse engineering, the team discovered that many hard drives have hidden vendor-specific commands that are not exposed through standard interfaces like SATA. These backdoor commands allow direct interaction with the drive's firmware through diagnostic ports. For instance, some drives include an RS-232 serial connection (similar to older modems) that can be accessed with a simple UART adapter. By connecting to this port, researchers can send low-level instructions that a normal computer would never be able to execute.
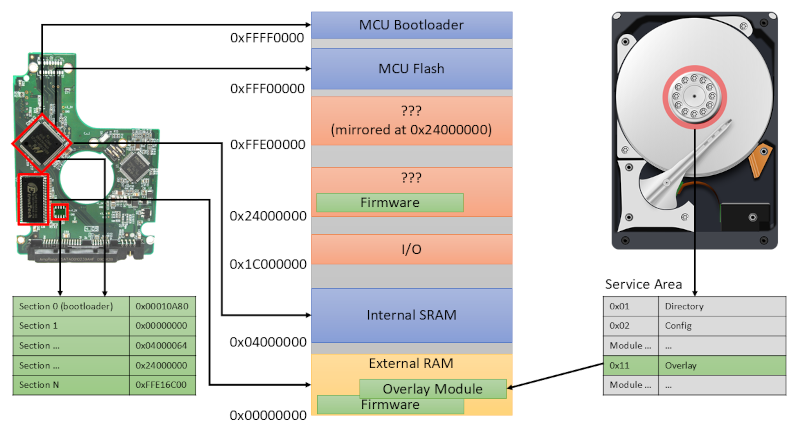
JTAG Access
Another route into the firmware is through JTAG (Joint Test Action Group) interfaces. JTAG is a standard for testing and debugging integrated circuits, and many hard drive controllers have JTAG pins on their circuit boards. By carefully soldering wires to these tiny points and using a JTAG programmer, an attacker can read or write the firmware directly, bypassing all security checks. This method requires significant technical skill and access to the drive's PCB.
The GitHub Repository
To document their findings, [I Code 4 Coffee] created a GitHub repository containing firmware dumps, notes, and scripts used during the analysis. This is an invaluable resource for anyone interested in hard drive firmware hacking. The repository includes examples of backdoor commands for specific drive models, as well as JTAG configuration files. By sharing this work, the hope is to build a community around this niche area of hardware security.
What We Can Learn from This Research
This deep dive into hard drive firmware teaches several lessons:
- Security through obscurity is fragile: Even consumer hard drives have multiple unadvertised interfaces that can be exploited.
- Data recovery tools have dual uses: The same PC-3000 that retrieves lost files can be used to dissect firmware.
- Legacy interfaces still matter: RS-232 and JTAG, though old, remain powerful entry points.
- Reverse engineering pays off: With patience and the right tools, you can understand—and modify—the very code that runs your storage devices.
Conclusion
Hard drive firmware hacking is not for the faint of heart, but as [I Code 4 Coffee] demonstrates, it can unlock surprising possibilities. Whether you're interested in backdoor commands, JTAG access, or simply want to explore the hidden layers of storage technology, this field offers a fascinating rabbit hole. The tools are available, the knowledge is being shared, and the potential for innovation—or exploitation—is huge. Just remember: messing with hard drive firmware can void warranties and risk data loss, so proceed with caution.